Identity-centric BYOD security
Close the last unmanaged gap—without invasive controls or complex deployment.
Why traditional MDM falls short for BYOD
A better approach to BYOD security
Aura’s solution combines our award-winning consumer protection with seamless, MSP-friendly deployment—eliminating headaches by balancing device security with employee privacy.
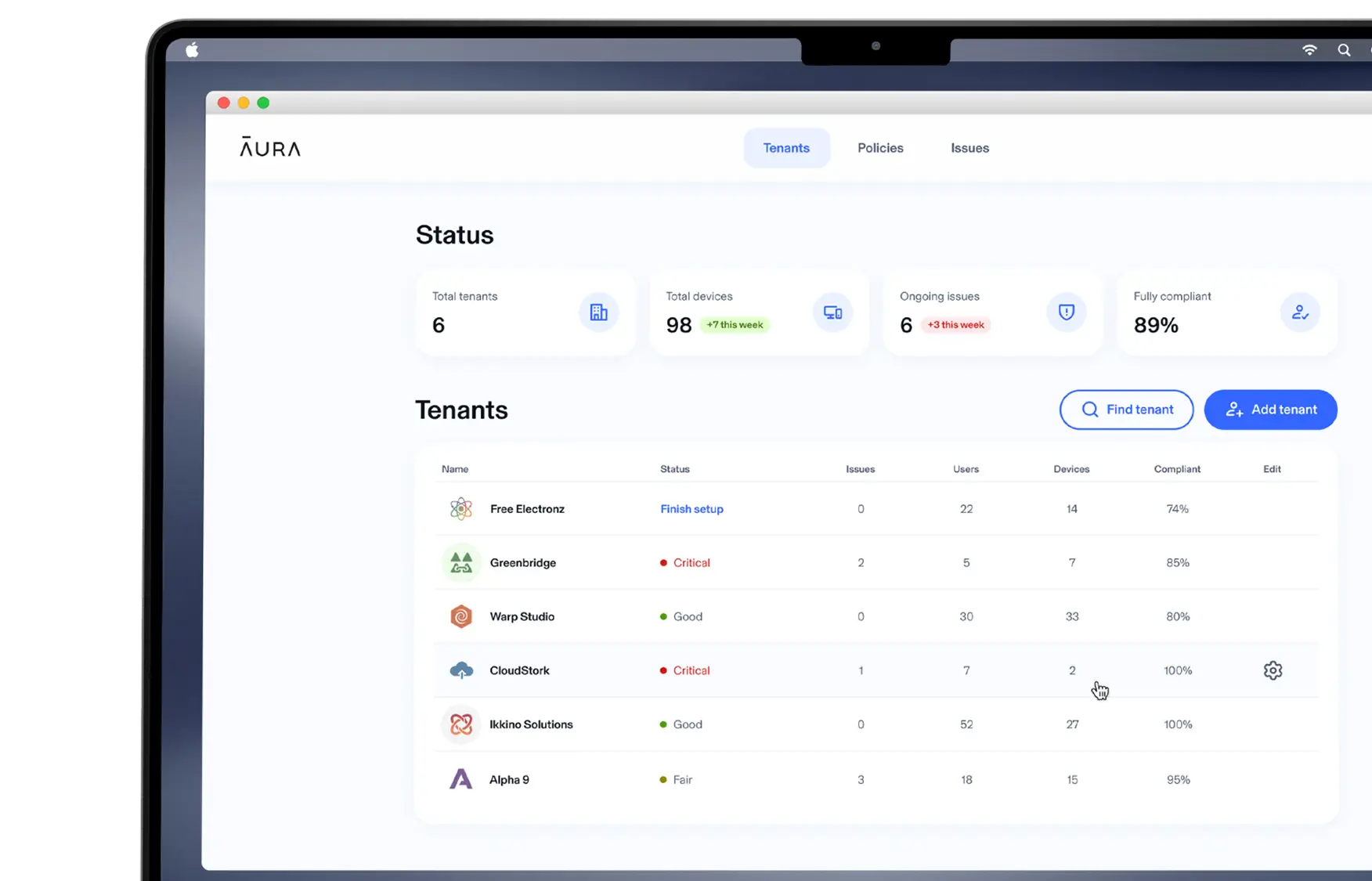
For MSPs
BYOD security that’s fast to deploy, easy to manage, and adopted by employees.
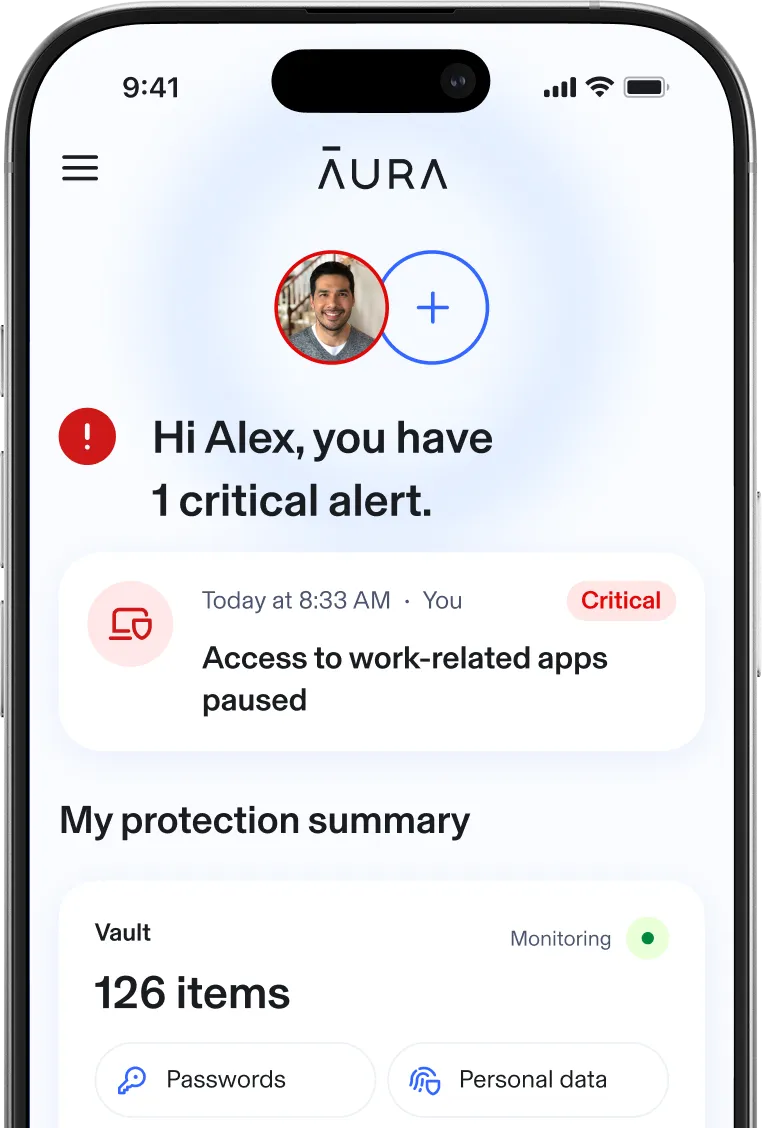
For employees
Personal protection that helps keep work and everyday data safe—built with privacy in mind.
Why MSPs choose Aura Business
- Fast deployment
Eliminate device enrollment and policy complexity.
- Effortless management
View everything from one lightweight console.
- Privacy-first design
Secures without intrusive device control or tracking.
- Identity-based protection
Help protect the person behind the device, not just the device.
- Increase adoption and trust
Employees are more willing to enroll when their privacy is respected.‡
- Revenue growth
Add new, high-margin protection services for clients.
Modern BYOD security vs. legacy MDM
Aura | Traditional MDM | |
|---|---|---|
Security model | Identity-centric (protects personal + work data) | Device-centric (locks down hardware) |
Privacy impact | Low: no visibility into personal data
or apps | High: invasive visibility into user activity |
Deployment | Lightweight install, low-touch provisioning | Complex agent enrollment |
Management | Simple dashboard, no constant oversight | Continuous monitoring &
policy enforcement |
Protection coverage | All-in-one protection — identity, passwords, PII, scams, fraud | Basic device compliance |
User experience | Light-touch, benefits the user | Controlling, invasive |