Digital Security 101

What To Do If Your Personal Information Has Been Compromised
Your personal information — including your email, phone number, and even SSN — can be compromised in a data breach or hack, putting you at risk of fraud.

Why Am I Getting So Many Spam Calls?
Your phone number is often leaked or sold, which makes it easy for scammers to spam you. Block unknown calls and protect your info to cut down on spam.

20+ Early Warning Signs That All Point to a Job Scam
It’s hard to spot a phony recruiter, if you don’t know what you’re looking for. Watch out for these red flags and learn how to identify job scams right away.

Unemployment Fraud: How Scammers Claim Benefits In Your Name
Unemployment scams lead to billions stolen in benefits and pandemic relief funds. But what happens when someone makes a claim under your name?

What is Smishing? How To Spot & Avoid The Latest Text Scams
Smishing — receiving scam texts pretending to be someone you trust — has increased over 328% in the last year! Here’s how to spot and avoid smishing scams.

How To Keep Your Kids and Teens Safe on Social Media
Social media safety for kids can be a confusing topic. Learn how to protect your children from the risks of social media and limit their screen time.

How To Identify a Fake Text Message Scam [With Examples]
Almost a quarter of all fraud cases start out as text scams. Learn how to quickly identify a fake text message scam and keep your phone (& finances) secure.

What Is Digital Security? Steps to Stay Safe Online (NEW)
The pandemic introduced us to remote socialization, school, work, and even healthcare. But have you truly mastered the art of digital security?
text

My Social Security Number Was Found on the Dark Web. Help!
Most SSNs have been leaked to the Dark Web in recent years — making it more important than ever to learn how to make yourself a less vulnerable target.

How To Detect Malware on Your Computer or Phone
Hackers only need a minute to wreak havoc on your finances and identity. Learn how to detect malware quickly and shut down cybercriminals.

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
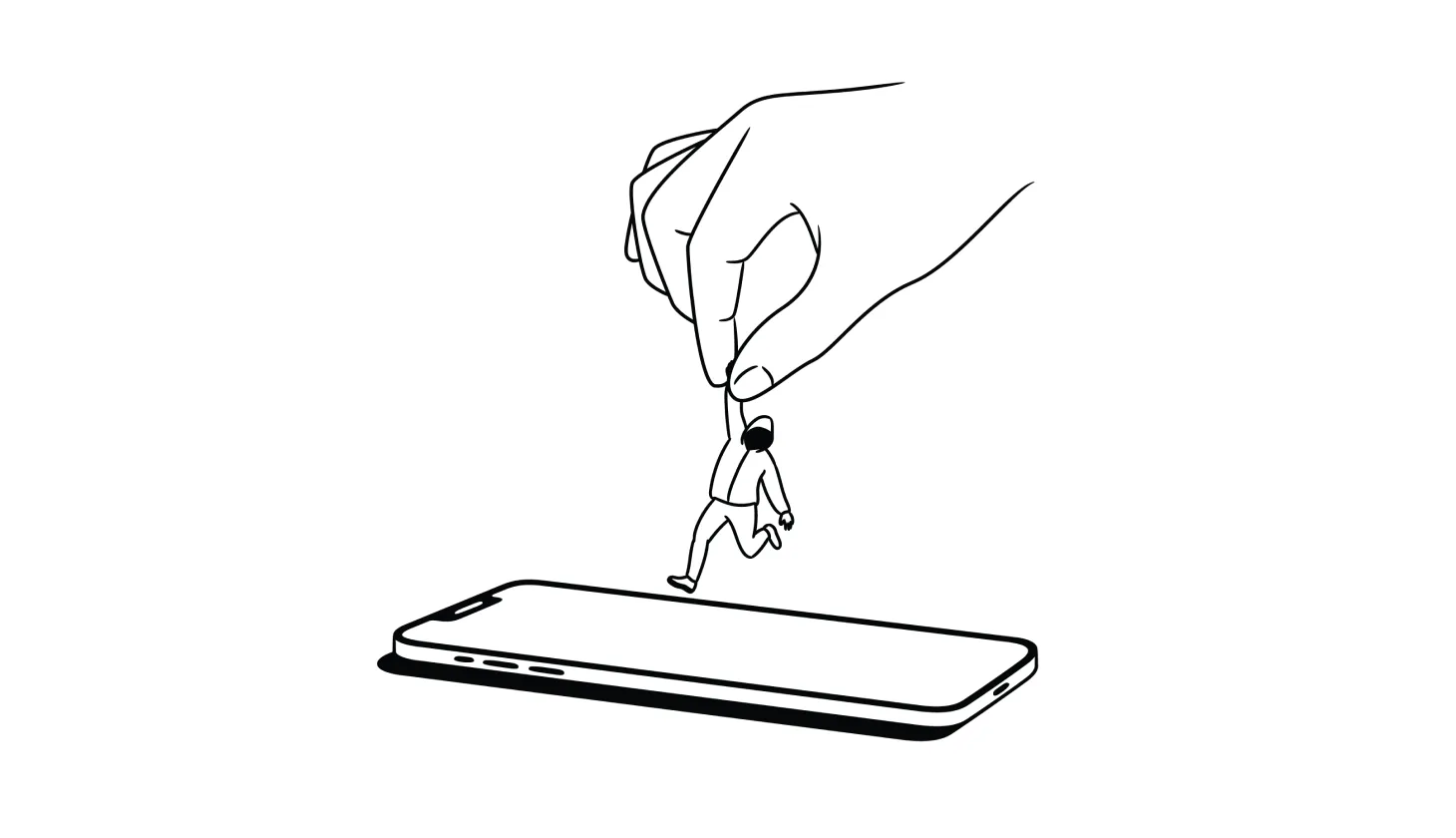
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).
.png)
.png)
.png)
.png)
.png)
.png)