Digital Security 101

What To Do If Your Personal Information Has Been Compromised
Your personal information — including your email, phone number, and even SSN — can be compromised in a data breach or hack, putting you at risk of fraud.

Why Am I Getting So Many Spam Calls?
Your phone number is often leaked or sold, which makes it easy for scammers to spam you. Block unknown calls and protect your info to cut down on spam.

How Hackers Get Into Your Computer (And How To Stop Them)
How do hackers get into your computer? Cybercriminals have numerous scams they can use to break into your device. Here’s how to keep them out.

How To Protect Your Social Security Number From Scammers
Do you know if scammers have your SSN? Learn how to protect your Social Security number and safeguard yourself against identity theft.

Credit Score vs. Credit Report: What You Need To Know
Learn the differences between your credit score and credit report, how they’re calculated, and what you can do to improve your credit today.

How To Avoid the 6 Latest Wells Fargo Scams
Wells Fargo scams can wipe out your savings with a single text message. Do you know the warning signs and how to stay safe?

The 7 Latest Amazon Scam Calls (and How To Spot Them)
Amazon phone scams are running rampant, with Americans receiving over 100 million every month. Learn how to identify the most common Amazon scam calls.

7 Signs of a Social Security Scam Call
Here’s what you need to know about Social Security scam calls and what to do if you realize you're on the phone with an SSA imposter.
text

My Social Security Number Was Found on the Dark Web. Help!
Most SSNs have been leaked to the Dark Web in recent years — making it more important than ever to learn how to make yourself a less vulnerable target.

How To Detect Malware on Your Computer or Phone
Hackers only need a minute to wreak havoc on your finances and identity. Learn how to detect malware quickly and shut down cybercriminals.

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
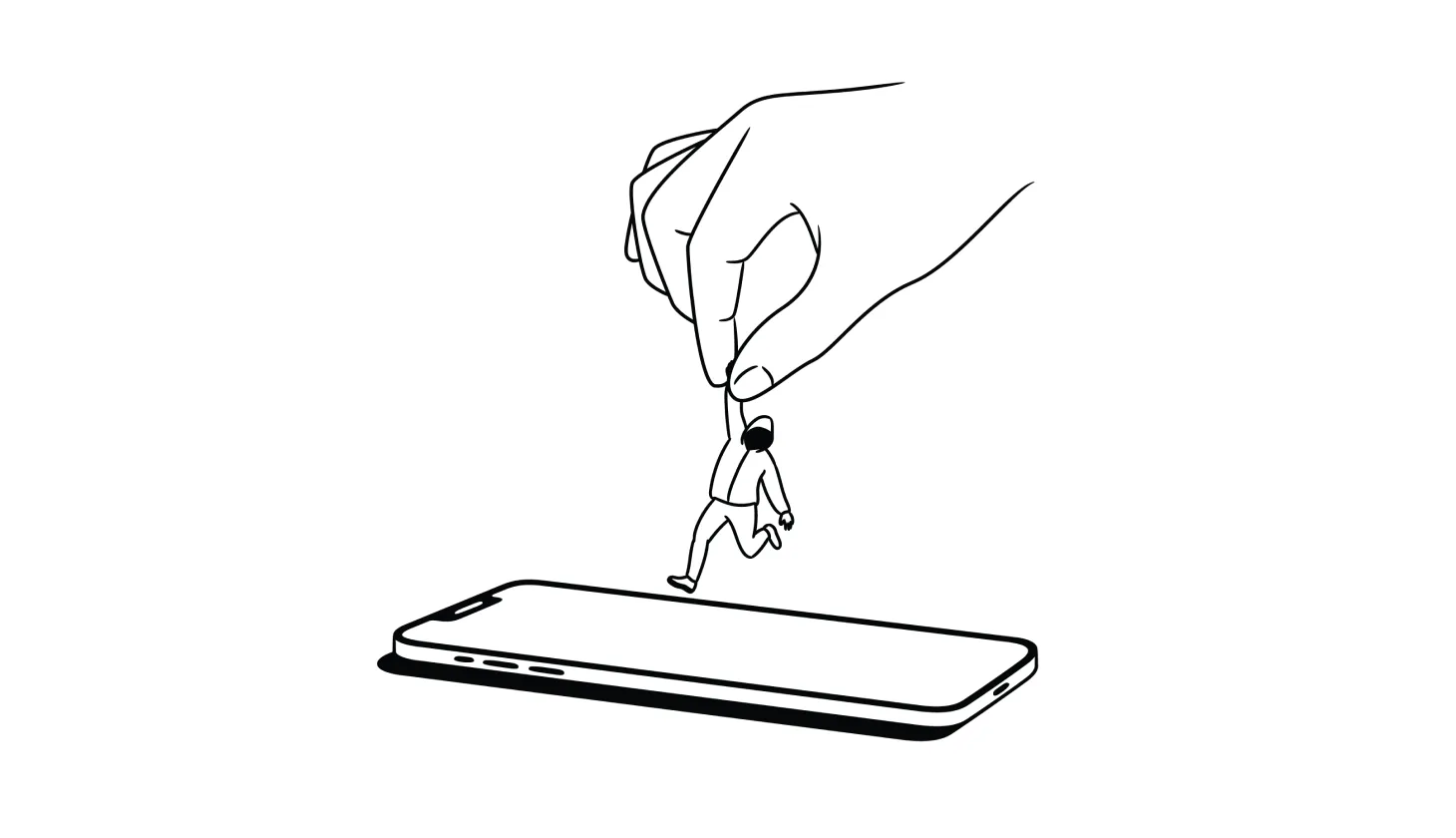
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).
.png)
.png)
.png)
.png)
.png)
.png)