Digital Security 101

Identity Theft Insurance Coverage, Limits, and Exclusions
Identity theft insurance helps reimburse stolen funds, legal fees, and other recovery costs associated with ID fraud. Coverage may vary by plan.

How To Block Ads on Chrome (Android, iPhone, and Desktop)
Google Chrome includes built-in tools to help block some ads and pop-ups — but a third-party ad blocker is a better bet for an ad-free browsing experience.

How To Detect Malware on Your Computer or Phone
Hackers only need a minute to wreak havoc on your finances and identity. Learn how to detect malware quickly and shut down cybercriminals.

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
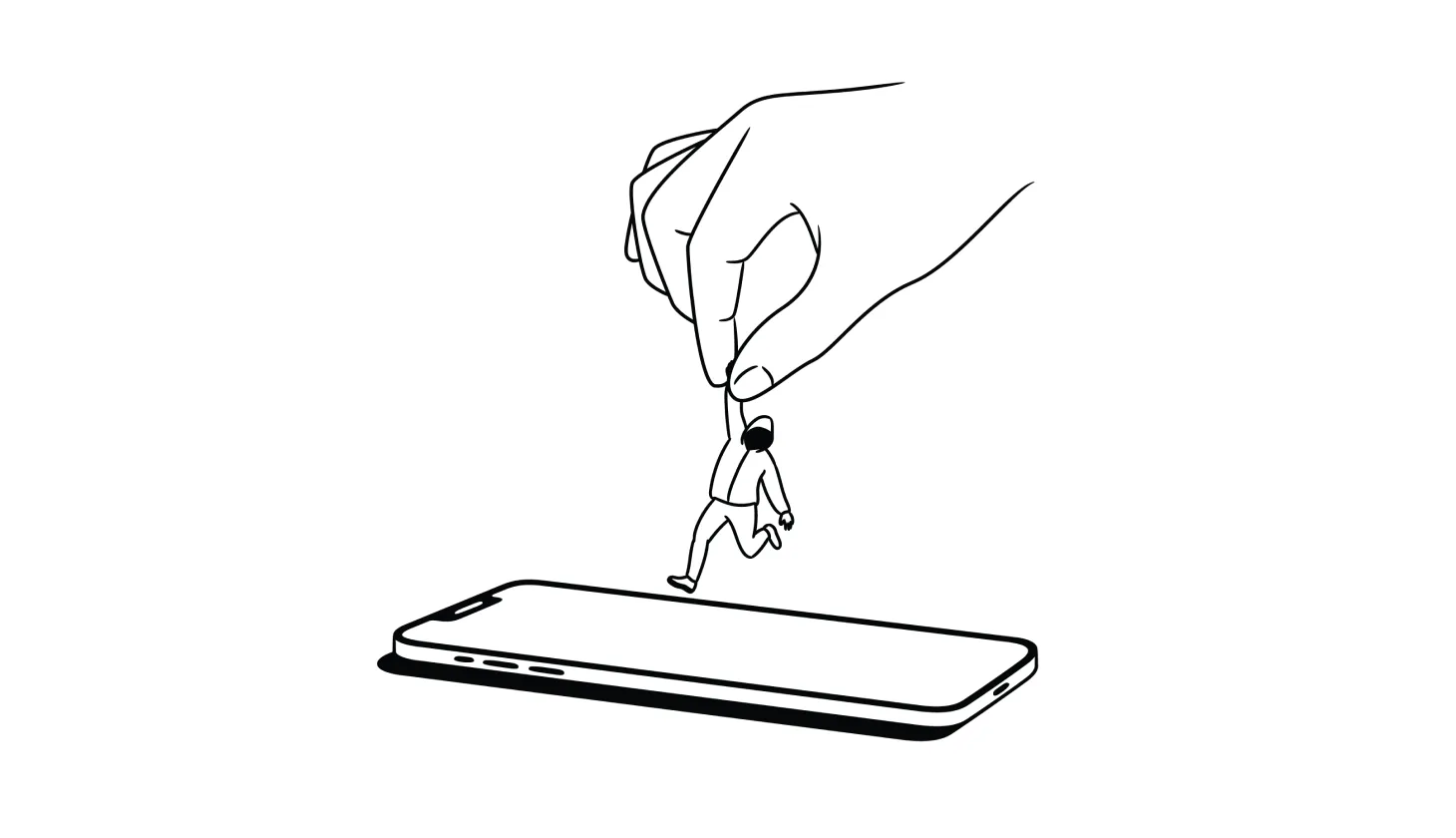
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).

USPhoneBook Opt Out Guide: How To Remove Your Info
USPhoneBook.com collects and shares personal data, which can put you at risk of harassment or even identity theft — unless you remove your information.
text

How To Remove Yourself From Data Broker Sites
Understanding privacy policies and opt-outs could be the only way to learn how to remove yourself from data broker sites.

How To Lock Your Credit With All Three Bureaus
Credit locks are one of the best tools available for protecting your credit file from fraud and errors — but are more complicated than a fraud alert.

Stolen Tax Refund Check? Here’s How To Get Your Money Back
Tax season is scam season. If someone stole your tax refund check or filed for one under your name, here's how you can get it back and protect yourself.

Loan Fraud Explained: How Scammers Get Free Money In Your Name
If a criminal steals your identity, they can get loans on cars, homes, and businesses in your name. Here’s how to stop loan fraud from happening to you.

Is Bark Worth It? What Parents Should Know Before Buying
Bark has been a leader in parental controls software for years — but many users complain about its functionality and how easy it is to circumvent.

Online Banking Security: How To Keep Your Accounts Safe
Banks spend millions on online security — but it’s not always enough to keep scammers out. Follow these steps to secure your online bank account.
.png)
.png)
.png)
.png)
.png)
.png)