Digital Security 101

How To Block Annoying Ads on YouTube
While you can pay for an ad-free YouTube experience with YouTube Premium, third-party extensions and privacy-focused browsers are often cheaper and better.

How To Block Ads (Easiest Methods For Each Platform)
Ads and pop-ups aren’t just annoying; they can also put your online privacy and safety at risk — luckily you can block them on almost every platform.

How To Spot a Scammer on a Dating Site: 9 Warning Signs
50% of Americans who have used a dating app in the past five years have experienced catfishing. Here’s how to spot a scammer on a dating site.

How To Recognize and Report Coinbase Scam Emails
Fraudsters use Coinbase scam emails to impersonate the company and dupe users into sharing login information. Here’s what can happen after.

The 7 Latest Chase Bank Scams (and How To Avoid Them)
Are you a Chase Bank customer? Don’t get scammed! Learn about the 7 latest Chase Bank scams (and how to avoid them).

Is Credit Monitoring Actually Worth It? How To Decide
Credit monitoring can protect you against fraud. But do you need to pay for it? Learn what credit monitoring does and how to decide if you need it.

How To Prevent Credit Card Fraud: 10 Essential Steps
Criminals use your physical card or stolen credit card numbers to make purchases in your name or impersonate you — here's how you can stop them.

How To Block Text Messages From Unknown Numbers (NEW)
Is your phone being bombarded with text messages from strangers? Learn the easiest ways to block text messages from unknown numbers.
text

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
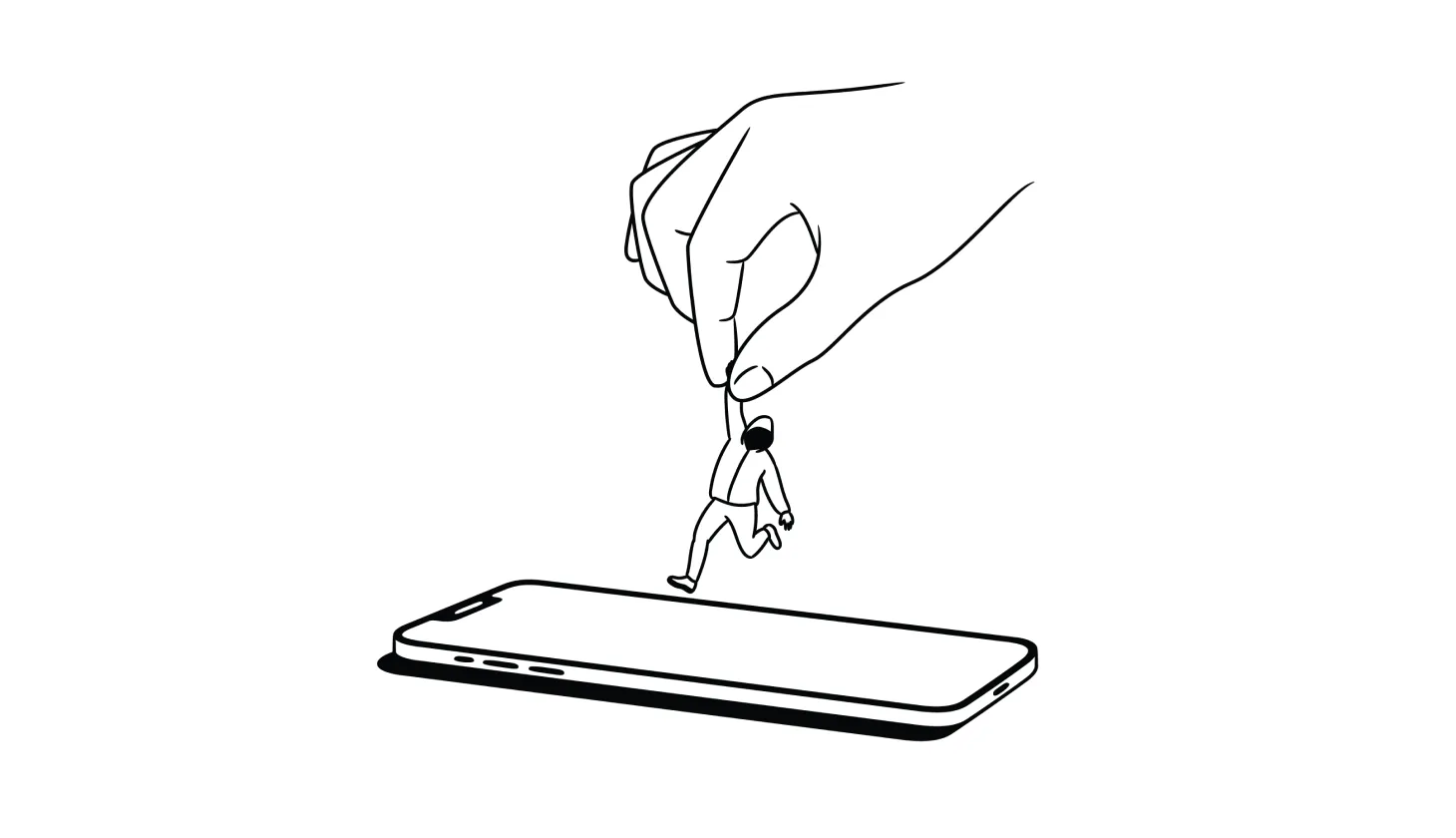
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).

USPhoneBook Opt Out Guide: How To Remove Your Info
USPhoneBook.com collects and shares personal data, which can put you at risk of harassment or even identity theft — unless you remove your information.

What To Do If Your Identity Is Stolen (2024 Identity Restoration Guide)
Knowing what to do if your identity is stolen makes the difference between a close call and financial ruin. Are you ready if a scammer strikes?
.png)
.png)
.png)
.png)
.png)
.png)