Digital Security 101

How To Block Annoying Ads on YouTube
While you can pay for an ad-free YouTube experience with YouTube Premium, third-party extensions and privacy-focused browsers are often cheaper and better.

How To Block Ads (Easiest Methods For Each Platform)
Ads and pop-ups aren’t just annoying; they can also put your online privacy and safety at risk — luckily you can block them on almost every platform.

How To Avoid the 8 Latest Zelle Scams (Updated)
Zelle is fast and easy to use. But is it safe? Here’s a list of the latest Zelle scams you need to watch out for and how you can keep your money safe.

How to Recognize & Avoid the 7 Most Common Geek Squad Scams
Geek Squad scams impersonate Best Buy employees to bilk innocent victims. Here are the 7 most common scams and how to spot them right away.

What Can a Scammer Do With Your Medicare Number?
Scammers use phishing tactics to trick victims into giving up their Medicare number — and then use it to steal health benefits or worse.

Is It Bad To Have Too Many Credit Cards?
Is it bad to have too many credit cards? There's no right or wrong answer, but your credit score may be impacted. Learn more with this essential guide.

Is Your Walmart Account Hacked? Here’s What To Do
If your Walmart account is hacked, unauthorized purchases are only one threat. Learn what to look out for and how to stop fraudsters.

12 Alarming Senior Citizen Scams: What You Need to Know
Older adults are less likely to spot the warning signs of scams early on or reach out for help when they've fallen victim.
text

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
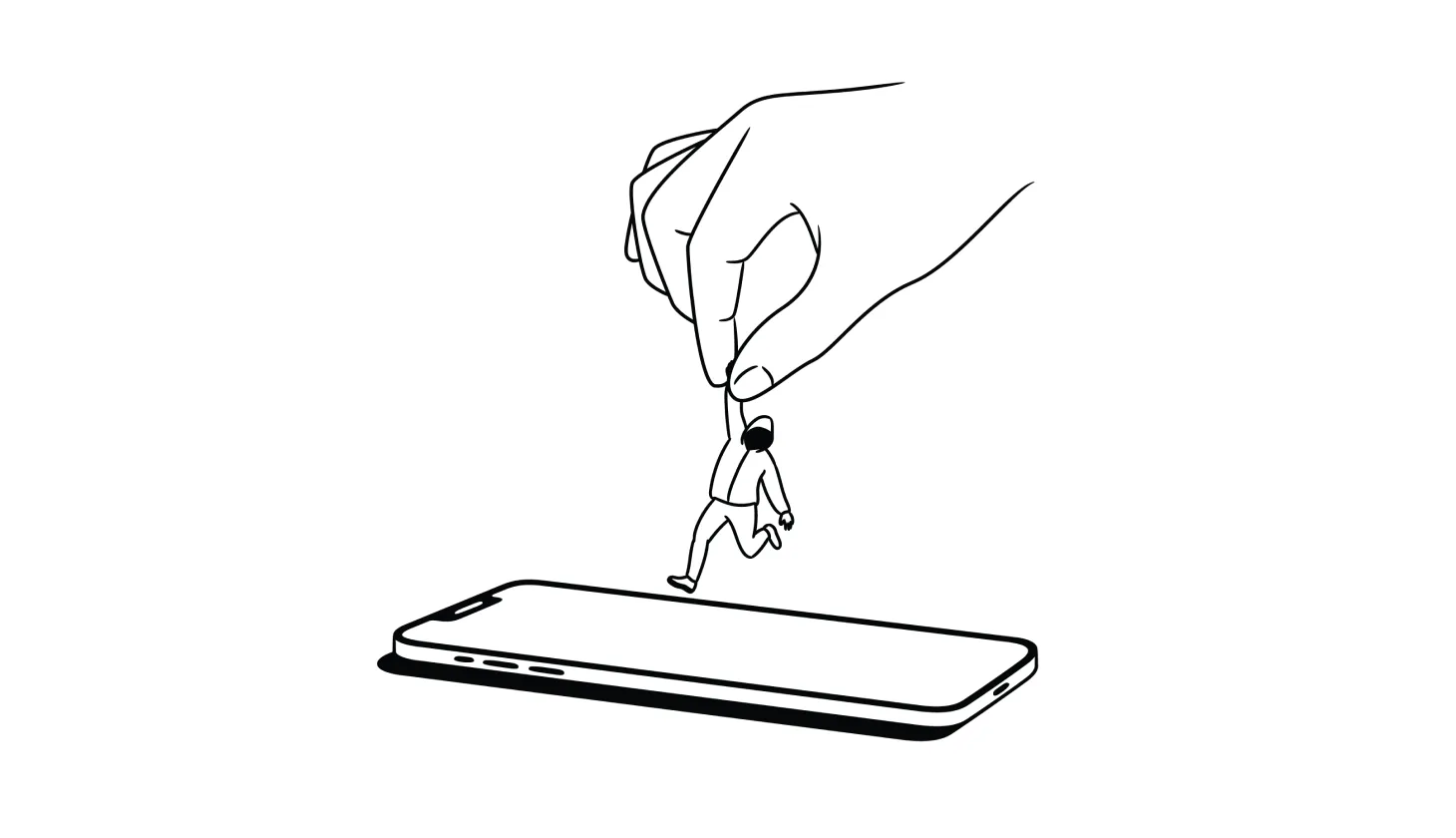
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).

USPhoneBook Opt Out Guide: How To Remove Your Info
USPhoneBook.com collects and shares personal data, which can put you at risk of harassment or even identity theft — unless you remove your information.

What To Do If Your Identity Is Stolen (2024 Identity Restoration Guide)
Knowing what to do if your identity is stolen makes the difference between a close call and financial ruin. Are you ready if a scammer strikes?
.png)
.png)
.png)
.png)
.png)
.png)