Digital Security 101

Aura vs. Bark: How To Choose the Best Parental Control App
Aura vs. Bark is a hot debate — which is the best parental controls app to keep your kids safe online? It’s time to find out.

Identity Theft Insurance Coverage, Limits, and Exclusions
Identity theft insurance helps reimburse stolen funds, legal fees, and other recovery costs associated with ID fraud. Coverage may vary by plan.

How To Screen Calls on Your iPhone (6 Methods)
There are multiple tools you can use to successfully screen calls on an iPhone, from iOS17’s new Live Voicemail feature to AI-powered third-party tools.

Help—My Debit Card Was Charged for Something I Didn’t Buy
If your debit card was charged for something you didn't buy, you must act fast. Fraudsters could have more of your personal info.

Types of Google Play Gift Card Scams and How to Report It
Common Google Play gift card scams employ a wide range of techniques — from phishing emails to elaborate social engineering schemes. Here’s what to do.

How To Tell If Your Wi-Fi Is Hacked (And How To Fix It)
Your Wi-Fi may be prone to hacking if you're still using your router's default credentials, haven't updated its firmware, or have remote management on.

What Can Someone Do With Your License Plate Number?
Fraudsters can’t find out your SSN or other sensitive information from your license plate number alone — but they can use it to scam or impersonate you.

How To Spot a Fake Bank Text Message Scam
Fake bank text messages are a form of smishing where fraudsters use texts to impersonate financial institutions and phish for PII.
text

How Does Identity Theft Insurance Work? Do You Need It?
Identity theft insurance may be a standalone policy or an add-on with your home insurance. What do these cover? How much do they cost?

Identity Theft Victim Assistance: How To Get Help
Are you the victim of identity theft or fraud? Here are the best resources to help you secure your identity, recover funds, and protect yourself.

My Social Security Number Was Found on the Dark Web. Help!
Most SSNs have been leaked to the Dark Web in recent years — making it more important than ever to learn how to make yourself a less vulnerable target.

How To Detect Malware on Your Computer or Phone
Hackers only need a minute to wreak havoc on your finances and identity. Learn how to detect malware quickly and shut down cybercriminals.

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
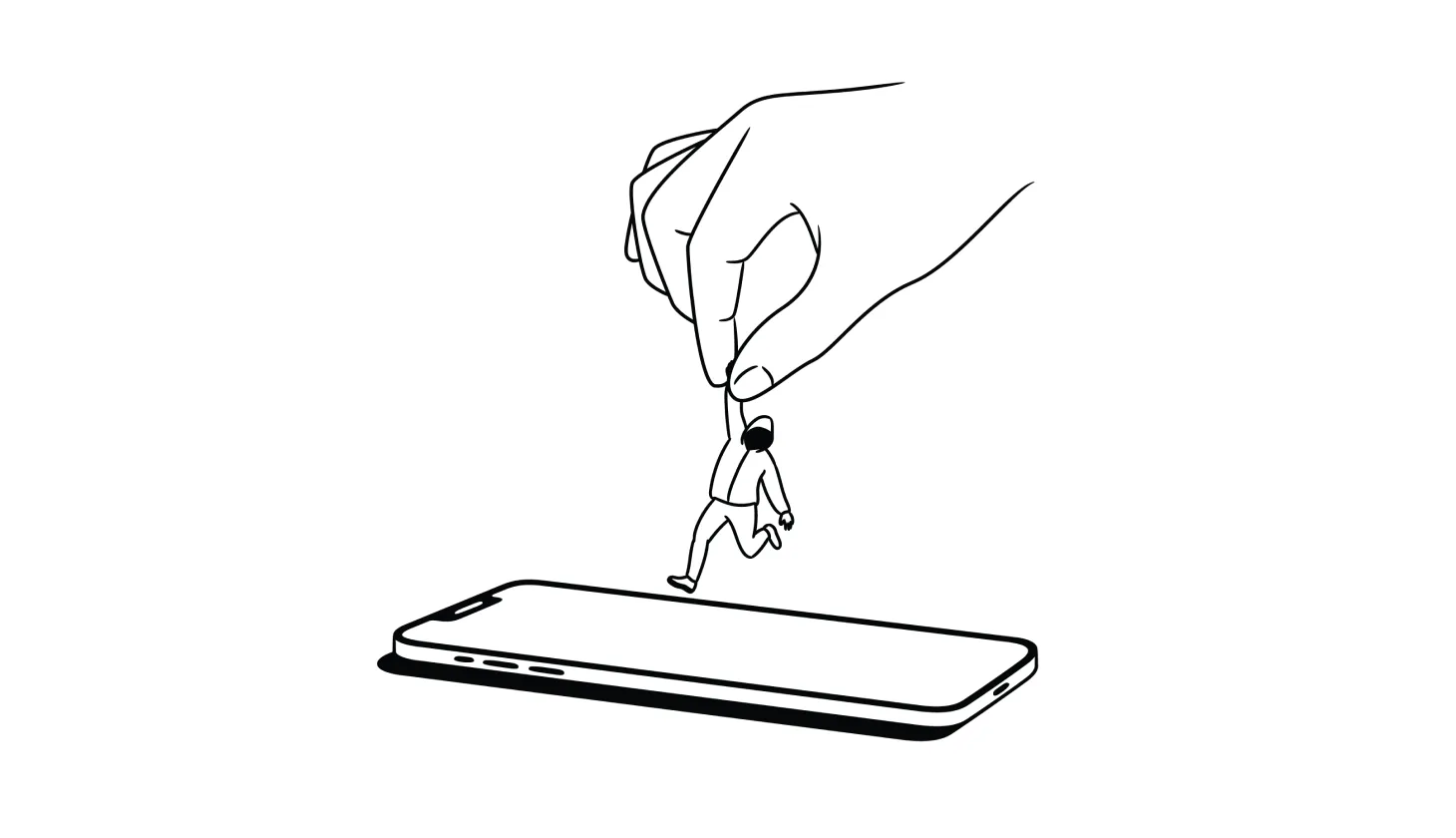
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.
.png)
.png)
.png)
.png)
.png)
.png)