Digital Security 101

How To Block Annoying Ads on YouTube
While you can pay for an ad-free YouTube experience with YouTube Premium, third-party extensions and privacy-focused browsers are often cheaper and better.

How To Block Ads (Easiest Methods For Each Platform)
Ads and pop-ups aren’t just annoying; they can also put your online privacy and safety at risk — luckily you can block them on almost every platform.

Why Do Scammers Want Gift Cards?
Is it safe to pay with gift cards? Learn the latest gift card scams and why scammers always seem to want gift cards.

How To Avoid the Worst Christmas Scams of 2023
Scammers have sunk to new lows this Christmas season, even targeting your grandparents. Learn how to protect yourself while shopping online this year.

Can Macs Get Viruses? How To Remove Malware From Macs
Yes, Mac computers can be infected with malware and other viruses. Learn how to identify a virus and safely remove malware from your Mac.

How To Identify (and Avoid) Apple Gift Card Scams
Did someone request payment with Apple gift cards? It’s most likely a scam. Learn the latest Apple gift card scams and what to do if you’ve been targeted.

15 Amazon Scams You Didn’t Know About (Until Now)
Amazon scams are on the rise. Get familiar with how common scams work to protect your family and finances.

What To Do If a Scammer Has Your Email Address
Your email address is a precious commodity for fraudsters. Here’s what you should do if a scammer has your email address to stay safe.
text

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
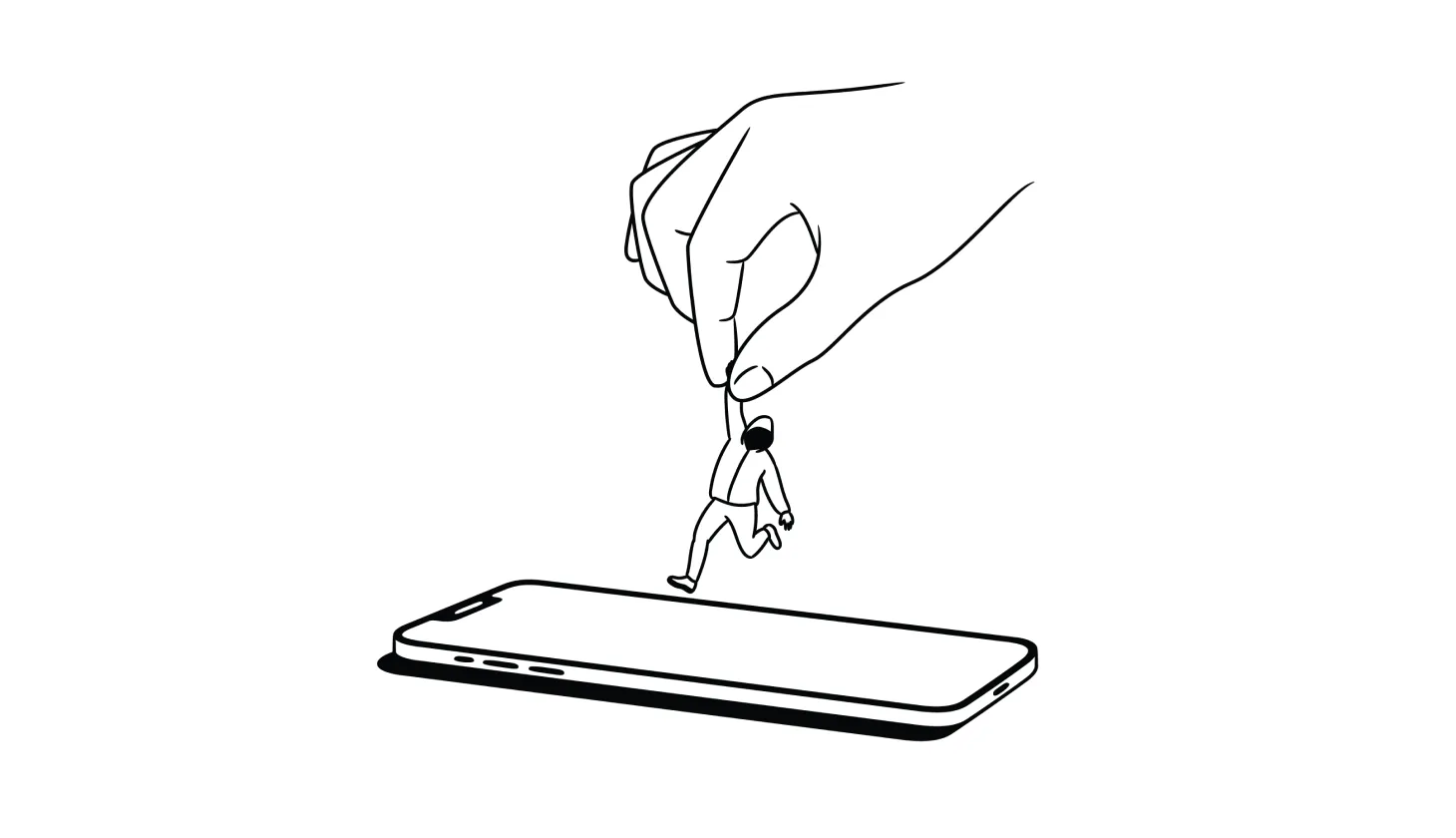
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).

USPhoneBook Opt Out Guide: How To Remove Your Info
USPhoneBook.com collects and shares personal data, which can put you at risk of harassment or even identity theft — unless you remove your information.

What To Do If Your Identity Is Stolen (2024 Identity Restoration Guide)
Knowing what to do if your identity is stolen makes the difference between a close call and financial ruin. Are you ready if a scammer strikes?
.png)
.png)
.png)
.png)
.png)
.png)