Digital Security 101

How To Block Ads on Chrome (Android, iPhone, and Desktop)
Google Chrome includes built-in tools to help block some ads and pop-ups — but a third-party ad blocker is a better bet for an ad-free browsing experience.

How To Remove Viruses From Mac Computers
Hackers use malware to infect your Mac, spy on you, or hold your sensitive files hostage — but with a few steps, you can clear your Mac of most infections.

Can Someone Hack My iPhone? How To Tell & What To Do
iPhones can’t be “hacked” in the traditional sense — but scammers have found numerous ways to access your data, photos, Apple ID, and other accounts.
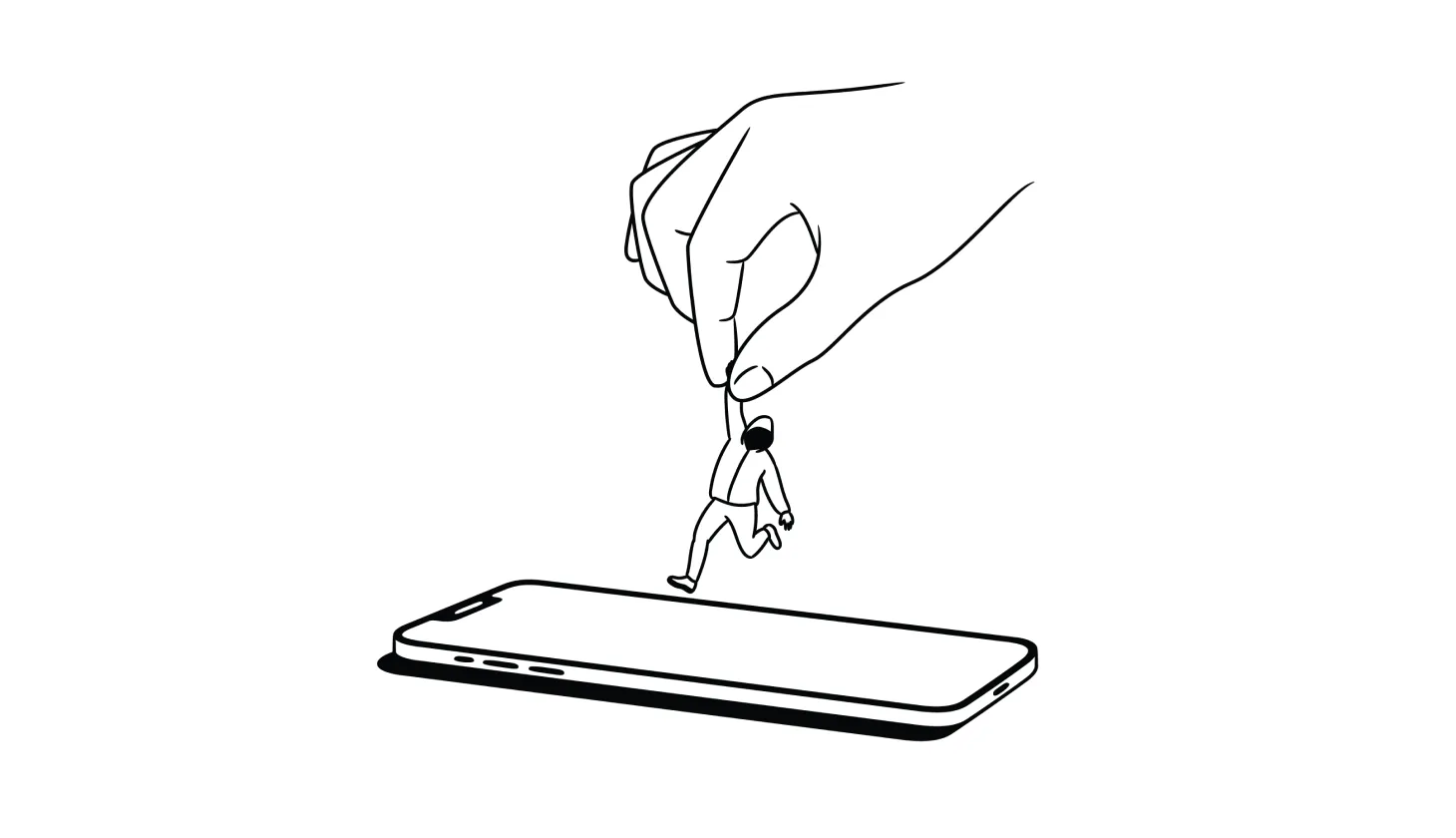
Answered: How To Remove a Hacker From Your Smartphone
Deleting suspicious apps, resetting your device, and recovering hacked accounts are among the best ways to remove a hacker from your smartphone.

Do You Need Antivirus? These Questions Can Help You Decide
With advances in built-in tools, many security experts claim you don’t need a third-party antivirus software provider. But that’s not the case for everyone.

How To Track Down Someone Who Scammed You (and What To Do Next)
Did you get scammed and want to find out who did it? Here’s everything you need to know about tracking down scammers (and what your options are).

USPhoneBook Opt Out Guide: How To Remove Your Info
USPhoneBook.com collects and shares personal data, which can put you at risk of harassment or even identity theft — unless you remove your information.

What To Do If Your Identity Is Stolen (2024 Identity Restoration Guide)
Knowing what to do if your identity is stolen makes the difference between a close call and financial ruin. Are you ready if a scammer strikes?
text

Is BeReal Safe For Kids? What Parents Need To Know
Despite its approach of prioritizing authenticity over sharing, BeReal has some privacy risks that might make you think twice about letting your kids use it.

What Is Saturn App? How To Know If It's Safe For Your Kids
While Saturn App is a popular calendar app for high school students, it has also come under attack by parents and school boards over privacy concerns.

How To Check If Someone Is Illegally Using Your Name
Stolen and leaked information can be used at any moment. Keep tabs on your identity by regularly checking the places where scammers may try to use it.

DeleteMe Alternatives: 7 Better Ways To Protect Your Privacy
DeleteMe was one of the first services to help you remove your personal info from data brokers — but some competitors do more to keep you safe online.

Should Kids Play Video Games? 10 Strategies for Safer Gaming
Research shows that video games can have both positive and negative effects on children — depending on how, when, and what games they play.

The Top 9 LifeLock Alternatives (Reviewed and Rated)
LifeLock is a well-known name in online security, but it’s not the only dependable choice for identity theft protection.
.png)
.png)
.png)
.png)
.png)
.png)